The Role of Hash-Based Algorithms in Ensuring Quantum-Resistant Security
Understanding Hash-Based Algorithms
The development of hash-based algorithms plays a significant role in achieving quantum-resistant security. As quantum computing advances, it poses a serious threat to traditional cryptographic methods like RSA and ECC. These classical algorithms, which have long been the backbone of digital security, are vulnerable to quantum computers that can solve their underlying mathematical problems efficiently. Hash-based algorithms offer a promising alternative, leveraging mathematical hash functions that are resistant to both classical and quantum attacks.
In regions like Saudi Arabia and the UAE, especially in dynamic cities such as Riyadh and Dubai, the need for robust cryptographic security is paramount. These areas are leading the charge in digital transformation and technological innovation. Implementing hash-based algorithms ensures that critical information remains secure, maintaining trust and compliance with international security standards. These algorithms use cryptographic hash functions to create unique, fixed-size outputs from variable-size inputs, making it computationally infeasible to reverse-engineer the original data, even with quantum computing capabilities.
Hash-based cryptographic methods, such as those used in the Merkle Tree and the Lamport signature scheme, provide a secure foundation for protecting sensitive information in a quantum-enabled future. Their resistance to both classical and quantum attacks makes them a critical component of next-generation cryptographic systems.
Challenges in Implementing Hash-Based Algorithms
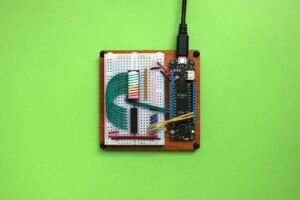
Implementing hash-based algorithms involves several challenges, but addressing these effectively is crucial for long-term security. One primary challenge is ensuring that these new encryption methods are compatible with existing systems while maintaining high performance and user experience. Organizations must meticulously plan and execute the integration of hash-based algorithms, including thorough testing and validation processes to prevent operational disruptions.
Effective change management is essential for the successful adoption of hash-based algorithms. Organizations need comprehensive strategies to manage the transition, including updating software, hardware, and security protocols. Training staff on the new encryption methods and their implications is also vital. Engaging executive coaching services can help leaders develop the skills necessary to oversee these changes, ensuring effective communication and alignment across teams.
Continuous monitoring and evaluation are necessary to maintain the effectiveness of hash-based algorithms. Organizations should establish robust procedures for regularly assessing and updating their security measures to keep pace with evolving quantum computing capabilities. Collaboration with management consultants and cybersecurity experts can provide valuable insights into best practices and emerging trends, helping organizations stay ahead of potential threats and ensuring the ongoing protection of sensitive data.
The Role of Leadership and Effective Communication
Effective leadership and management skills are critical for the successful implementation of hash-based algorithms in safeguarding sensitive information. Leaders must be equipped to manage technological transitions, including strategic planning, stakeholder engagement, and effective communication. Executive coaching services can help leaders develop the necessary skills to navigate these changes and drive successful outcomes in the adoption of advanced encryption technologies.
Clear and effective communication is vital during the transition to hash-based algorithms. Leaders must ensure that all stakeholders understand the importance of these new encryption methods and the steps being taken to implement them. This includes explaining the potential risks of quantum computing to existing cryptographic systems and the benefits of adopting hash-based algorithms. By fostering a culture of transparency and collaboration, organizations can facilitate smoother transitions and achieve greater buy-in from employees and partners.
Management consulting provides valuable support in aligning organizational strategies with the latest advancements in cybersecurity. Consultants can offer insights into best practices for integrating hash-based algorithms, optimizing security measures, and ensuring compliance with regulatory standards. By combining these resources with strong leadership, organizations can enhance their security posture and achieve successful outcomes in their digital transformation efforts.
The Integration of AI and Blockchain
Artificial Intelligence (AI) and Blockchain technology play significant roles in enhancing cryptographic security through hash-based algorithms. AI can be leveraged to develop and refine these encryption algorithms, providing adaptive security solutions that respond to new threats. Machine learning models can analyze data patterns to detect and mitigate potential security breaches, ensuring that sensitive information remains secure.
Blockchain technology complements hash-based algorithms by offering a decentralized and tamper-proof ledger for recording transactions and data exchanges. Integrating Blockchain with cryptographic systems ensures data integrity and transparency, as any attempt to alter or corrupt information can be easily detected. This combination of technologies provides a robust framework for securing digital assets and enhancing the overall security posture of organizations.
Generative AI also contributes to the development of innovative encryption methods. By exploring new algorithmic approaches, generative models can create advanced hash-based solutions that offer enhanced security features. Leveraging these technologies allows organizations to stay ahead of emerging threats and ensure the ongoing protection of their digital assets.
#HashBasedAlgorithms, #QuantumResistantSecurity, #CryptographicSecurity, #AIinCybersecurity, #BlockchainTechnology, #GenerativeAI, #LeadershipInTech, #ChangeManagement, #BusinessSuccess