The Cornerstone of Digital Rights Management
Understanding Access Control in DRM
Access control in DRM (Digital Rights Management) is a critical component that ensures only authorized users can access and use digital content. By managing permissions and restrictions, access control protects digital assets from unauthorized use, distribution, and piracy. This advanced permissions management is vital for content creators, publishers, and businesses to safeguard their intellectual property and maintain control over their digital products. Access control mechanisms in DRM include authentication processes, encryption, and the assignment of user roles and permissions, ensuring that sensitive data remains secure and only accessible to legitimate users.
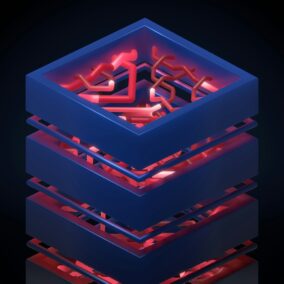
Implementing Effective Access Control Strategies
Implementing effective access control strategies involves multiple layers of security to protect digital content from unauthorized access. The first layer is user authentication, which verifies the identity of users attempting to access the content. This can include passwords, biometric verification, and multi-factor authentication (MFA), providing robust security against unauthorized access. Once authenticated, users are granted specific permissions based on their roles and requirements, ensuring that they can only access the content and functionalities necessary for their purposes. Role-based access control (RBAC) and attribute-based access control (ABAC) are commonly used models that assign permissions based on user roles and attributes, respectively, providing a flexible and scalable approach to access management.
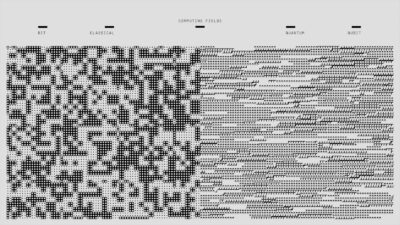
The Role of AI and Blockchain in Enhancing Access Control
Modern technologies such as Artificial Intelligence (AI) and blockchain are revolutionizing access control in DRM by introducing more sophisticated and secure mechanisms. AI-powered access control systems can dynamically adjust permissions and detect anomalies in user behavior, enhancing security and preventing unauthorized access. For instance, machine learning algorithms can analyze access patterns and flag suspicious activities, enabling proactive threat detection and response. Blockchain technology, with its decentralized and immutable ledger, provides a transparent and tamper-proof method for recording access permissions and transactions. This ensures that access control policies are consistently enforced and that any changes to permissions are transparently logged and auditable.
Access Control in Saudi Arabia’s Digital Ecosystem
Saudi Arabia is at the forefront of adopting advanced digital technologies, including robust access control mechanisms in DRM, to protect its burgeoning digital economy. The Kingdom’s Vision 2030 initiative emphasizes the importance of cybersecurity and digital transformation, driving the adoption of cutting-edge access control solutions across various sectors. For instance, in the financial sector, banks and financial institutions are leveraging access control technologies to secure sensitive customer data and ensure compliance with regulatory requirements. Similarly, in the healthcare sector, access control mechanisms are used to protect patient records and ensure that only authorized medical professionals can access sensitive information, thereby safeguarding patient privacy and enhancing the security of healthcare systems.
Access Control Innovations in the UAE
The UAE is also a leader in embracing modern access control solutions to protect its digital assets and ensure the security of its information infrastructure. In Dubai, the Smart Dubai initiative is leveraging access control technologies to enhance the security and privacy of its smart city projects. This includes implementing AI-driven access control systems that can adapt to evolving threats and ensure that only authorized users can access critical infrastructure and services. Additionally, the UAE’s government and private sectors are utilizing blockchain-based access control solutions to enhance transparency and trust in digital transactions, ensuring that access permissions are securely managed and auditable.
Best Practices for Implementing Access Control in Businesses
For businesses looking to implement effective access control in DRM, several best practices can help ensure robust security and compliance. Firstly, conducting a thorough risk assessment to identify potential vulnerabilities and determine appropriate access control measures is crucial. This involves evaluating the sensitivity of digital content and the potential impact of unauthorized access. Secondly, businesses should implement multi-factor authentication (MFA) to strengthen user authentication and prevent unauthorized access. Regularly reviewing and updating access permissions based on changes in user roles and responsibilities is also essential to ensure that access control policies remain relevant and effective. Finally, businesses should invest in advanced access control technologies, such as AI and blockchain, to enhance security and stay ahead of evolving threats.
Conclusion: Securing Digital Content with Access Control
In conclusion, access control in DRM is a fundamental aspect of securing digital content and protecting intellectual property in the digital age. By managing permissions and restrictions, access control ensures that only authorized users can access and use digital assets, safeguarding against unauthorized use and distribution. With the integration of modern technologies such as AI and blockchain, access control mechanisms are becoming more sophisticated and resilient, providing robust security for digital ecosystems. As Saudi Arabia and the UAE continue to lead the way in digital transformation, adopting advanced access control solutions will be critical to ensuring the security and integrity of their digital assets and supporting their ambitious visions for the future.
Future Prospects: Innovations and Opportunities
Looking ahead, ongoing innovations in access control technology will unlock new opportunities for enhancing digital security, enabling organizations to adapt to evolving threats and capitalize on emerging trends. By leveraging the power of AI and blockchain, businesses can implement more sophisticated and resilient access control solutions, ensuring that their digital content remains secure and their intellectual property rights are protected. As the digital economy continues to evolve, access control in DRM will remain a vital tool for safeguarding digital assets and maintaining the integrity and value of digital content in an increasingly interconnected and data-driven world.
—
#AccessControl #DigitalRightsManagement #DRM #DataProtection #ContentSecurity #Cybersecurity #UserPermissions #DigitalContent #InformationSecurity #DigitalAccess #AI #Blockchain