Navigating the Regulatory Landscape with Robust Encryption Techniques
Encryption: A Cornerstone of Data Protection Compliance
In today’s data-driven world, complying with stringent data protection regulations is a top priority for organizations across the globe. Encryption stands as a cornerstone of these efforts, providing a robust defense against unauthorized access to sensitive information. By transforming data into an unreadable format, encryption ensures that even if a breach occurs, the compromised information remains inaccessible to malicious actors.
Compliance Frameworks: A Global Perspective
Various data protection regulations, such as the European Union’s General Data Protection Regulation (GDPR), the California Consumer Privacy Act (CCPA), and the Health Insurance Portability and Accountability Act (HIPAA) in the United States, mandate the implementation of appropriate security measures, including encryption, to protect personal and sensitive data. Adhering to these frameworks not only safeguards customer trust but also shields organizations from hefty fines and reputational damage.
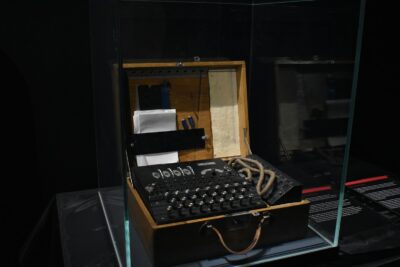
Encryption Algorithms: Choosing the Right Tool for the Job
Selecting the appropriate encryption algorithm is crucial for achieving effective data protection. Symmetric encryption, utilizing a single key for both encryption and decryption, is often favored for its speed and efficiency in securing large volumes of data. Asymmetric encryption, employing a pair of keys (public and private), offers enhanced security for data transmission and digital signatures. Organizations must carefully assess their specific needs and risk profile to determine the most suitable encryption algorithm for their data protection strategy.
Encryption Key Management: The Linchpin of Security
The effectiveness of encryption hinges on the secure management of encryption keys. Robust key management practices, including the generation, storage, rotation, and destruction of keys, are essential to maintain the confidentiality and integrity of encrypted data. Organizations should consider implementing hardware security modules (HSMs) or cloud-based key management systems (KMS) to ensure the highest level of security for their encryption keys.
Encryption in Transit and at Rest: Comprehensive Data Protection
Data protection compliance necessitates safeguarding data both in transit and at rest. Encryption in transit, typically implemented through protocols like Transport Layer Security (TLS), ensures that data transmitted over networks remains confidential. Encryption at rest, applied to data stored on servers, databases, or other storage media, prevents unauthorized access even if the physical storage is compromised. By employing encryption for both scenarios, organizations can establish a comprehensive data protection framework.
Encryption and Cloud Computing: Addressing Unique Challenges
The increasing adoption of cloud computing introduces unique challenges for data protection. While cloud providers offer robust security measures, organizations must ensure that their data remains encrypted even when stored in the cloud. Encryption key management becomes particularly critical in cloud environments, as organizations must maintain control over their keys to ensure data confidentiality and comply with regulatory requirements.
Encryption Beyond Compliance: Building Trust and Resilience
While compliance with data protection regulations is a legal necessity, the benefits of encryption extend far beyond meeting regulatory obligations. Robust encryption practices build trust with customers and partners, demonstrating a commitment to safeguarding their sensitive information. Additionally, encryption enhances organizational resilience by mitigating the impact of data breaches and minimizing the risk of financial loss, reputational damage, and legal liabilities.
The Future of Encryption: Adapting to Evolving Threats
As cyber threats continue to evolve, so too must encryption technologies. Quantum computing, with its potential to break current encryption algorithms, poses a significant challenge. However, researchers are actively developing quantum-resistant encryption algorithms to ensure the long-term security of sensitive data. Organizations must stay informed about emerging encryption technologies and adapt their data protection strategies accordingly to maintain robust security in the face of evolving threats.
Encryption as a Business Enabler: Unlocking Opportunities
Encryption is not merely a security measure but also a business enabler. By safeguarding sensitive data, encryption fosters trust and confidence among customers, partners, and stakeholders. This trust can translate into increased business opportunities, as organizations that prioritize data protection are often favored by customers who value privacy and security. Moreover, robust encryption practices can help organizations avoid costly data breaches and the associated financial and reputational damage, ensuring business continuity and resilience.
The Role of Leadership in Data Protection Compliance
Effective data protection compliance requires a commitment from the highest levels of leadership within an organization. Leaders must champion a culture of security awareness and prioritize the implementation of robust encryption measures. By investing in the necessary resources, technology, and training, organizations can create a data protection framework that aligns with regulatory requirements and safeguards sensitive information, ultimately contributing to long-term business success and resilience in an increasingly data-centric world.
#Encryption #DataProtection #Compliance #Cybersecurity #PrivacyRegulations #DataSecurity #InformationSecurity #GDPR #CCPA #HIPAA #CloudSecurity